Simplify Breach Prevention and Response with Automated Data Breach Analysis
Data Breach Analysis
Automate the analysis of data breaches, whether preemptively or post-incident, offering transparent insights into the extent of the breach, its financial ramifications, and global regulatory responsibilities. Guarantee precise and prompt notifications to individuals affected by the breach, ensuring comprehensive communication and adherence to regulatory obligations.
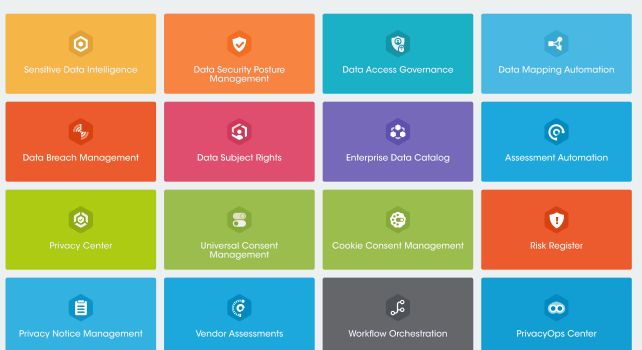
Key Features
Automate Impact Discovery
Leverage people data graphs to pinpoint specific individuals affected by a breach across all interconnected systems. This advanced identification mechanism ensures a granular understanding of the impact, allowing organizations to swiftly and accurately assess the scope of compromised information. By harnessing the power of interconnected data graphs.
DepthImpact Analysis
Delve deeply into the specific data elements compromised during a breach, conducting a thorough analysis to identify the exact nature and extent of the compromised information. This detailed examination enables organizations to ascertain the specific datasets that may have been exposed, offering a targeted and precise response.
Broad System Coverage
Native compatibility with a diverse array of structured and unstructured data systems is readily available out of the box, spanning across multicloud environments, SaaS applications, on-premises infrastructure, and various data warehouses. This comprehensive support ensures seamless integration and data accessibility.
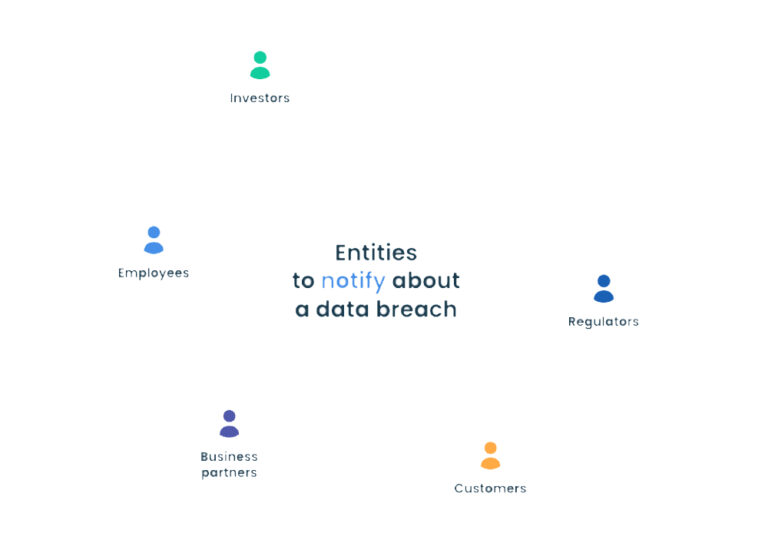
Customize Notifications
Efficiently generate precise notifications promptly through the use of customizable templates. This feature allows organizations to tailor notification messages to specific incidents or communication needs, ensuring clarity and relevance. By leveraging customizable templates, the notification process becomes streamlined and adaptable.
Discover Impacted Individuals and Data
Harness the power of People Data Graphs to automatically pinpoint exact individuals affected by a data breach, mitigating the risks associated with both over-notification and under-notification. This advanced mechanism ensures a nuanced understanding of the impact, enabling organizations to tailor their response strategies with precision.

Scalable Across Multiple Data Systems
The inherent support for numerous structured and unstructured data systems ensures that breach analyses encompass expansive hybrid cloud environments seamlessly. This includes thorough coverage of Software as a Service (SaaS), Infrastructure as a Service (IaaS), data clouds, and on-premises infrastructure.
Precise Data Breach Impact
Identify and detect specific personal data elements that have been compromised or stolen, enabling a detailed understanding of the breach impact in accordance with relevant regulations. This granular analysis ensures compliance with data protection laws by providing insights into the compromised data’s sensitivity.

Global Regulations Covered
Automate the process of discovering global regulations pertinent to an organization’s compliance obligations, driven by the affected individual’s location and specific regulatory mandates. By integrating location-based data into the compliance framework, this automated approach ensures a dynamic and precise identification of applicable regulations.

Covering Everywhere You Have Data
With 1000+ integrations across data systems